Hidden File System Reader is a free portable command line rootkit scanner for Windows, which is gonna look for infections in hidden filesystems created by malware. The only thing that you need to do in order to start scanning with Hidden File System Reader is double click on the executable. After that all you’re gonna see is a log file created in the same directory where the executable is and that’s it.
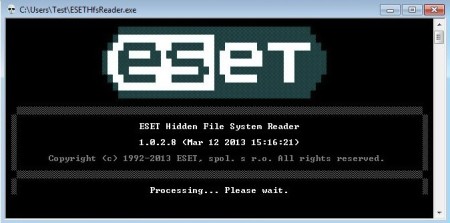
This is pretty much the only thing that you’re gonna see from Hidden File System Reader. How long the scan will last depends on the size of your hard drives and also on the severity of the malware infection.
Similar software: Trend Micro RootkitBuster, BitDefender Rootkit, Sophos Anti-Rootkit.
Make sure that when you’re running this free hidden filesystem rootkit scanner that you’re not starting it from somewhere where files can’t be written or created. We already mentioned that log file is going to be created and if you run Hidden File System Reader somewhere without write permissions, log won’t be created, and you won’t be able to know what the scan results were. Key features of Hidden File System Reader are:
- Free and simple to use – you just have to click on the executable
- Allows you to scan hidden file systems infected with rootkits/malware
- Portable – doesn’t require installation – can be used from USB drive
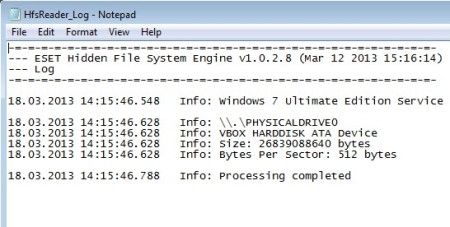
- Detailed scan report – log file is created after scan completes
Something that not many people are aware of is the fact that certain types of Windows rootkits can create their own partitions or filesystems on the hard drive, without the user knowing about it. This is gonna be a hidden partition, and not only that, it’s also gonna be encrypted. You can probably guess what’s gonna be kept there, original versions of the rootkit, in case that it gets deleted and removed.
How to scan for hidden file systems and partitions infected with rootkits using Hidden File System Reader
Instructions for starting the scan are pretty simple, download the executable and double click on it. Those are the only two things that you need to do, no additional config, setup or anything like that is necessary.
Scan will probably be over very quickly, that is if you don’t have any kind of infections or anything like that on your system. Depending on what’s found, what kind of hidden filesystems and partitions, with what kind of encryptions and infections, scan might take a bit longer. Created log file will have detailed report on what was found and what kind of actions were taken. It can be found in the same directory where the Hidden File System Reader executable was activated.
Conclusion
Hidden File System Reader will help you make sure that after you’ve gotten rid of a nasty rootkit infection that no left-over surprises were left. Even if you don’t notice anything strange happening, the infection might still be available somewhere in the background. By scanning your system for hidden partitions, they can be detected in time, before causing new outbreaks and problems for your system. Give it a try and see what’s really going on behind the scenes.