Microsoft Attack Surface Analyzer is a free tool from Microsoft to identify changes in attack surface caused by installation of any software. This tool is for IT testers and developers, so that they can test their applications, before releasing them to publick.
Here is a description of Attack Surface Analyzer from MSDN blog:
The Attack Surface Analyzer beta is a Microsoft verification tool now available for ISVs and IT professionals to highlight the changes in system state, runtime parameters and securable objects on the Windows operating system. This analysis helps developers, testers and IT professionals identify increases in the attack surface caused by installing applications on a machine.
The tool takes snapshots of an organization’s system and compares (“diffing”) these to identify changes. The tool does not analyze a system based on signatures or known vulnerabilities; instead, it looks for classes of security weaknesses as applications are installed on the Windows operating system.
The tool also gives an overview of the changes to the system Microsoft considers important to the security of the platform and highlights these in the attack surface report. The Microsoft Security Development Lifecycle (SDL) requires development teams to define a given product’s default and maximum attack surface during the design phase to reduce the likelihood of exploitation wherever possible. Additional information can be found in the Measuring Relative Attack Surface paper.
Some of the checks performed by the tool include analysis of changed or newly added files, registry keys, services, ActiveX Controls, listening ports, access control lists and other parameters that affect a computer’s attack surface.
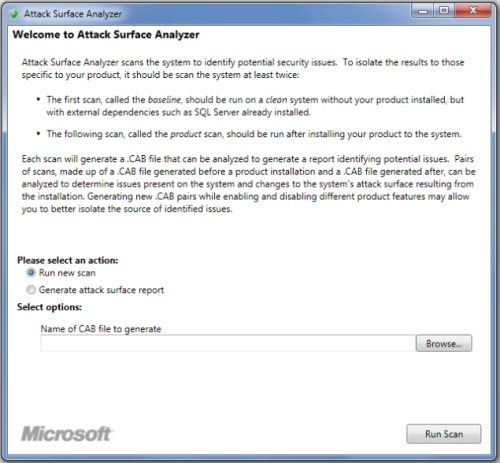
Microsoft Attack Surface Analyzer is quite easy to use. To see impact on attack surface because of any installation, just do a before and after scan with this tool, to see the differrences.
How to use Microsoft Attack Surface Analyzer:
Step 1: Download and install Microsoft Attack Surface Analyzer. It can be downloaded from here.
Step 2: Do a scan of the system with Attack Surface Analyzer. This tool will generate a report of the tool in form of a .CAB file. You can open that report with any unzip software, like 7-zip.
Step 3: The unzipped report will be in form of an XML file. You can open that in any notepad editor, or in a specialized XML editor for better formatting.
Step 4: Then install the software that you want to test.
Step 5: Then run Attack Surface Analyzer again, so that it can do a scan of the system. This scan will show all the changes to the attack surface that were made by installation of the software that you are trying to install.
As you see, Attack Surface Analyzer is quite easy to use. This tool was being internally used by Microsoft till now, and has been released to the developer community. It is still in beta.
Some other testing tools we reviewed earlier include: QMTest, Test Management software, and cross browser testing tools.