Flan Scan is a free open source network vulnerability scanner that you can use. It used be a internal tool used for scanning networks at Cloudflare HQ but now they have released it as an open source tool so more people can use it. You can just grab its source code and then use it in your network to scan potential vulnerabilities and see the report. Basically, it is a wrapper of Nmap and uses its commands under the hood. In the end, it creates a LaTeX report that it saves locally and you can also opt to push that report to a GCP or AWS Bucket.
If you work in network security kind of field then you will like this powerful network utility. Here you can use it to easily scan a network by giving a list of IP addresses and get the results. It can scan open ports, services with their versions, and relevant CVEs affecting your current network. It creates a beautiful report that you can export and use that wherever you like. This is the very simple use case of this tool. If you want then you can go with the advanced usage and use it in the real world scenario.
Using this Open Source Network Vulnerability Scanner from Cloudflare:
Flan Scan is a simple and powerful tool you can use to scan a network by giving it a file containing the list of IPs. After that, you can simply start the scan and see the results. The best way to install this network vulnerability scanner is through Docker. And there is a single command you have to run in order to use it. In my case, I will be installing this on my computer running MX Linux.
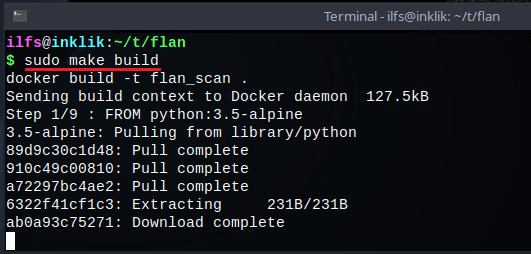
To install Flan Scan on your machine, you simply run the following command. Wait for the installation process to finish and then you are all ready to use it. but make sure that you have Docker installed and updated. If you don’t have Docker then you can install that using Snapcraft or you can see this post for the detailed instructions.
sudo make build
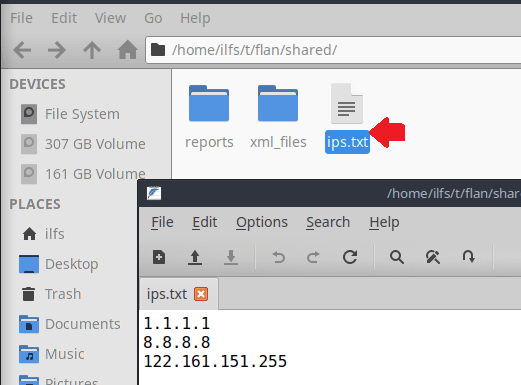
Now, when the installation part is done, here you will have to enter the list of IP addresses that you want to scan, Define those IP addresses sin the shared/ip.txt file. Enter the IP addresses one per line and then save the changes. The IP file looks like this.
Now, you can simply run the following command to start the scan. It will pick up each IP from the file and will do the scan. It does the serious scan on the IP that you have specified. After running the command, it wills can will show you the LaTeX output. You can copy the TeX data from here or you can simply find it in the reports folder which is in the shared directory.
sudo make start
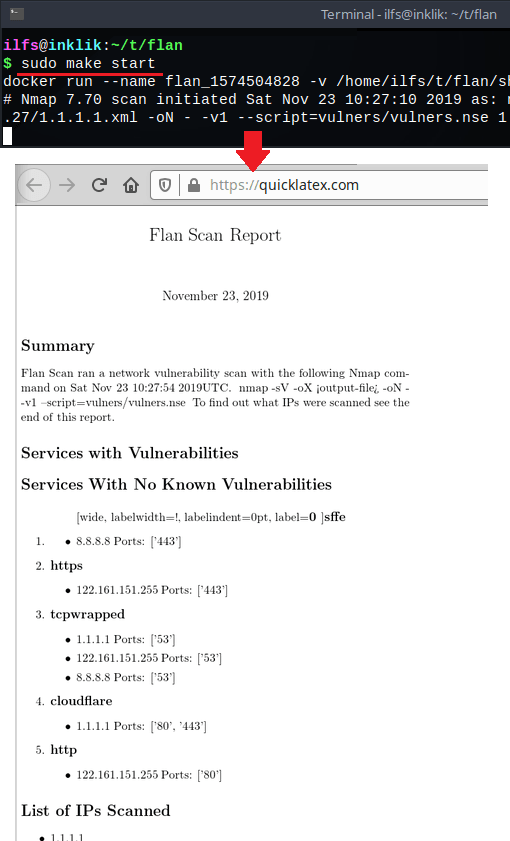
In this way, you can use this simple and powerful network vulnerability scanner easily. You only have to use a few command sin order to install it and scan a network. If you are a bit technical person then you can easily install and use it. Otherwise, if you just follow the given instruction then you will be able to easily deploy it on your machine. After getting the report in LaTeX, you can simply do whatever you want. You can sue some online LaTeX viewer websites to analyze the report or there are some software to do that as well.
Closing thoughts
If you are in a network security line of work then you may like the tool that Cloudflare just open sourced. You just get the Flan Scan on your machine and use it to see if it meets your requirements. Some advanced usage options are on its GitHub page and you can also see some of its other technical aspects there. The installation part is easy and I liked the fact that it supports GCP and AWS integration to save the reports online.