Have you ever wondered, when you enter your credit/debit card details, or your Social Security Number on a website that requires you to do so, how safe are they? How do you know that online shopping website where you’re entering your bank account number, is really that shopping portal, and not some scammer sitting in a garage waiting to siphon off all the money? Don’t be spooked. Read on to find out.
Web (Browser) Security Certificates: The authenticating documents of the web:
Web security certificates might not be something that you see on a daily basis while going on with your daily activities on the web, but they play an integral part in ensuring your confidential information remains confidential and does not fall into wrong hands. In one of my previous articles in this series titled ILFS Explains, I stressed the importance of browsing the Internet carefully and relying on only those websites that are HTTPS secured, especially the ones that require you to entire confidential information. Well, HTTPS is just one part of the picture. In fact, the secure socket layer (SSL) of the Web, is the one that, combined with security certificates does the real job. Security certificates thus, basically form the core of the technology that makes the websites you visit on a daily basis, actually secure.
Put simply, a Web Security Certificate is a validated electronic document, that is provided to a website (or the organization that owns it) by a trusted third party, known as the CERTIFICATION AUTHORITY. This E-document or the certificate is the identification that establishes the said website as a genuine one (and not a counterfeit). Sounds confusing? The following points should help in clarifying the matters. They explain how this whole system of certificate issuance works, in the simplest of words.
- A website (or the organization that owns it), requests a trusted third party known as CERTIFICATION AUTHORITY (CA), for a secure web certificate. For the same, it provides the certification authority with various credentials supporting its identity (For example: The Website’s name, home server location, Website owning organization’s address).
- Apart from all the above information, the website also provides the CA a very long password sort of thing, called the PRIVATE KEY. This is provided to the CA by the website, so that the CA essentially binds the website with this Private Key, which is known only to the website, and now to the CA.
- After this, the Certification Authority creates a secure digital document for that website, encrypting it with the provided PRIVATE KEY. Then, the CA packages this secure digital document with another key, called the PUBLIC KEY, and digitally signs it. This is what you call a Browser Certificate. This public key is another password kind of thing, the difference is, it is used to decrypt the data encrypted with the private key. The reason for using public key and not the private key is simple, Private Key is not meant to be shared, it’s owner exclusive, and hence, cannot be copied. On the other hand, Public Key acts as a sort of one way access key.
Ok, so the website’s got the digital certificate from a trusted third party CA. How does this authenticate the website?
The process that follows is simple. Whenever your Web browser visits a website, it’s presented with the digital certificate. And it uses it to establish the website’s authenticity. The following pointers should clarify.
- A user visits a secure website with a valid digital certificate. In turn, the website presents the browser with its valid digital certificate, as a proof of its authenticity.
- The Web Browser cross checks this certificate and the Electronic signatures of the CA against its own certificate collection. Almost all browsers come pre-packaged with hundreds of certificates from all major CAs for this purpose.
- The browser is also presented with the Public Key to decrypt the information. Since the public key decryption works only for the data encrypted by the private key associated with it (Public and Private keys are paired with each other), the browser knows that the website is indeed, what/who it claims to be.
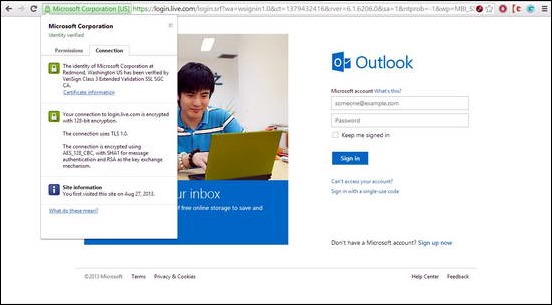
Here’s how a valid HTTPS Secured website appears to the browser. Clicking the well known padlock icon (location – browser dependent) reveals information about the Certification Authority
The above information (revealed by clicking the padlock icon) details the following information:
- The identity of the website has been verified by VERISIGN INTERNATIONAL CLASS 3 CA (VeriSign being the CA here). So the website is indeed authentic
- The connection to the website, and hence all data sent through, is encrypted via 128 bit encryption.
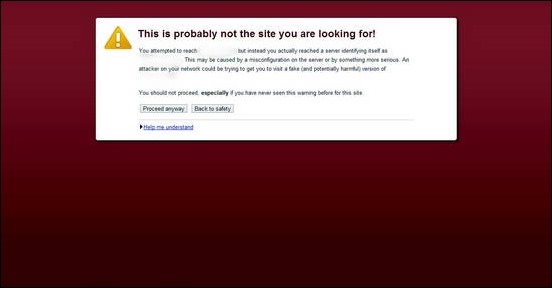
On the contrary, if the digital certificate used by the websites appears to be expired, or issued by a not so known provider, the browser blocks access to it and generates a warning for you to either stop or tread cautiously. See the screenshot:
The HTTPS information also shows that the certification doesn’t match. See, now this is why Certificates are important. They are the electronic documents that establish websites as genuine ones, or scams.
Conclusion
Digital Web Security Certificates are the authenticating credentials of the websites we visit on a daily basis. They play a crucial part in making the Web a more secure place. It’s clear that you should tread very carefully when visiting websites that have expired or non valid certificates. While all of them may not be scams, most of them are. Additionally, you should always take care and ensure that any site that requires you to input sensitive user data is a HTTPS secured one with a valid certificate. Because if it isn’t, it’s most likely to be a scam. That’s how Digital Security Certificates make your daily online transactions, your Facebook updates, and your tweets, amongst other things a satisfying experience.
What do you guys think about Web Security certificates? Do you take care in accessing the websites that don’t have valid ones? Do let me know in the comments below
Image Courtesy: Flickr Creative Commons.