This tutorial will explain Two Step Authentication in Amazon Web Services.
Two Step Authentication in Amazon Web Services help users to add an extra layer of protection to their AWS account and for AWS Identity and Access Management (AWS IAM) users created in their account. After enabling this two step verification, you will be asked for an authentication code after providing username and password, then only you will be able to access your account. Thus, it ensures more security and that’s why it is also known as AWS Multi-Factor Authentication (AWS MFA).
Amazon offers a huge range of web services, like Amazon S3, Amazon EC2 etc., and you can manage access to AWS resources with the help of Amazon IAM. To enable this two factor verification in AWS for free, a virtual AWS MFA app is needed.
Other applications that supports ‘Time-Based One Time Password’, like Authenticator for Windows phone, and Google Authenticator for iPhone and Blackberry etc. can also be used for AWS MFA. Using an associated application, you will be able to receive security codes to access your Amazon Web Services account.
In above screenshot, you can see that after enabling AWS MFA, you first need to enter username and password, and then you have to provide the required authentication code.
Enable Two Step Authentication in Amazon Web Services:
Steps to enable two step authentication in Amazon Web Services account as well as for AWS IAM are very simple. It is similar to, Google 2 step verification, Two factor authentication in Hotmail, Yahoo! two step verification, and two step authentication in Dropbox. One big difference is that you don’t need to provide your phone number for AWS MFA.
Step 1: It is a basic step where you need to access aws homepage and login to your account. You can sign in with you Amazon.com account.
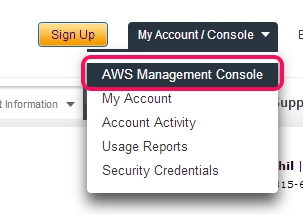
Step 2: After accessing your AWS account, access AWS Management Console.
Step 3: Clicking on AWS console will open a new page where you will find IAM option (highlighted in below screenshot) that will let you access IAM dashboard.
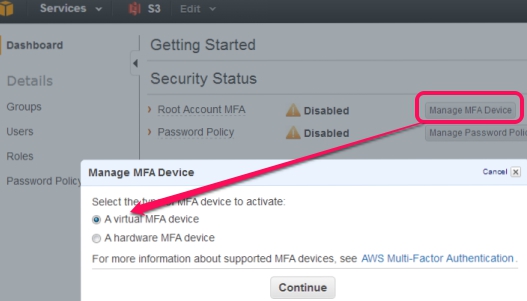
Step 4: This step lets you manage security status of your AWS account. After accessing IAM dashboard, tap on Manage MFA device button available in Security Status and you will find two options, like it is visible in below screenshot.
AWS MFA supports hardware as well as virtual MFA device. If you select hardware MFA device, then you have to purchase authentication device. So use first option; A virtual MFA device and continue the Two Step Authentication in Amazon Web Services.
Note: After choosing virtual MFA device, make sure that you have installed a virtual AWS MFA compatible application on your smartphone, like Google Authenticator on your android or iPhone.
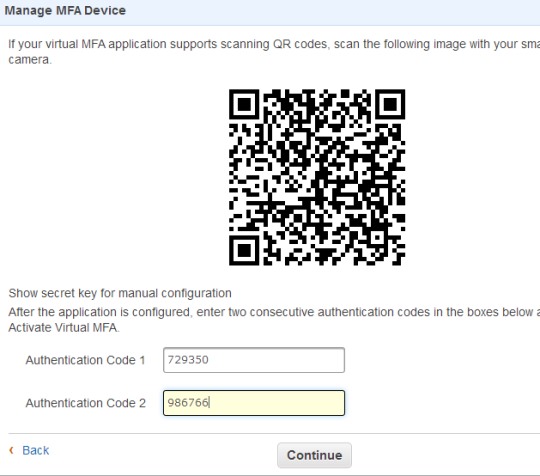
Step 5: It’s a very important step as you have to set up an account using the installed AWS MFA compatible application. Simply scan the barcode that will come in front of your PC screen using the application. Immediately after scanning the barcode, the application will provide you an authentication code on your smartphone. And after a short delay, you will find second code too.
Provide both codes and hit Continue button to complete the Two Step Authentication in Amazon Web Services.
Now you can check Security Status from IAM dashboard and you will find that AWS MFA is now enabled for your AWS account.
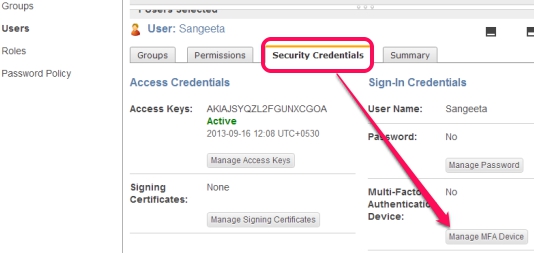
Apart from this, if you want to enable multi-factor authentication for a particular user, then on IAM dashboard, click on Users available at left side, select a user, and then access Security Credentials tab. Now you will be able to manage MFA device for selected user.
Process is similar, like it is for AWS account. You need to select virtual MFA device, and scan the barcode to get authentication codes. Finally, you will manage MFA device for that particular user.
Conclusion:
Two Step Authentication in Amazon Web Services surely provides stronger security than simple username and password. Even if your password is compromised somehow, then security code will be needed to access your account. Make sure you have enabled AWS Multi-Factor authentication to your AWS account and for AWS IAM users to increase the protection.