You are no longer safe online folks, because there is a new villain in town. Researchers at Google have recently discovered yet another (Haven’t forgotten Heartbleed and Shellshock, have you?) security issue in the obsolete and problematic SSL v3. This thing (Wait for it) called “Padding Oracle On Downgraded Legacy Encryption” (or POODLE, for all you pooch lovers) allows man-in-the-middle attacks. Using POODLE, hackers can extract sensitive data (e.g bank details) from secured online connections, mostly through compromised public Wi-Fi hotspots.
So what is Poodle?
Basically, it allows hackers to “force” your browser to revert to using the outdated SSL 3.0, instead of the more secure TLS. So, if you’re using a browser that supports SSL 3.0 (which includes pretty much every browser), the only way out is to remove the SSL 3.0 support from your browser. Confused? Let’s get to the details!

How Can You Protect Yourself Against POODLE?
Browser vendors have yet to develop fixes to address this security issue. So essentially, there is no concrete solution as of now. As it is a loophole in the protocol design, anyone using SSL 3.0 is vulnerable. Nonetheless, there are certain precautions that you can take to safeguard yourself against this threat. If you are using the most up-to-date browsers, and don’t use public Wi-Fi hotspots that much, it is unlikely that you will take the hit. However, you can never be too safe, so let’s see what can be done:
The best preventive measure is to disable/remove SSL 3.0 support from your browser, as this eliminates the possibility of being forced to downgrade to it. At the same time, you should enable TLS 1.0 (Transport Layer Security) in your browser.
Also see: Internet Explorer Bug Lets Hackers Access you PC Remotely
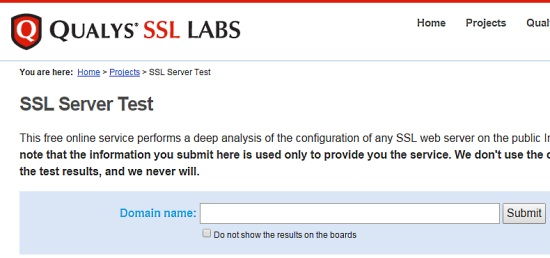
You can also check if a website uses SSL 3.0 by using Qualys SSL Labs tool. If it does, it might be already affected and it goes without saying, that you should steer away from that website!
Disabling SSL 3.0 Support In Different Browsers:
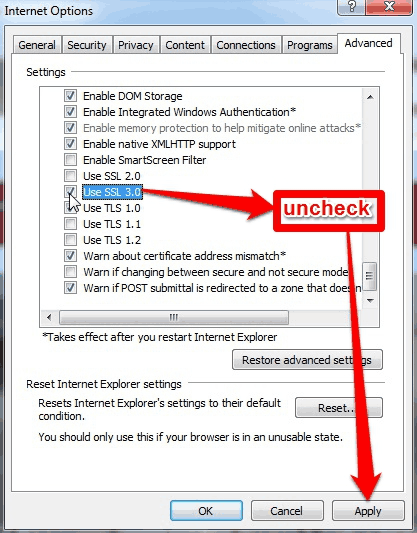
1. Internet Explorer
In order to disable SSL V3 in Internet Explorer, launch Internet Options from the Start Menu. Go to the Advanced tab, and uncheck the “Use SSL 3.0” option. Click Apply.
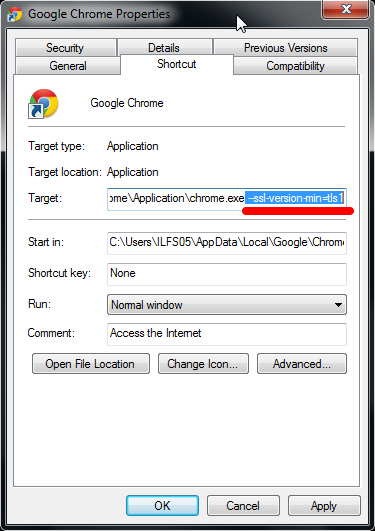
2. Google Chrome
Google is already developing a patch that would prevent its Chrome browser to revert to using SSL 3.0. But as of now, there is no specific option to prevent Chrome from using SSL 3.0. However, you can tell Chrome not to use SSL 3.0. In order to do so, right click on the Chrome shortcut on your desktop. Then go to Properties > Shortcut.
In the Shortcut tab, click inside the Target field, scroll all the way down to the end, and enter “ –ssl-version-min=tls1” without the quotes. However, note that this will only work if you launch Chrome from the Desktop shortcut.
Firefox
SSL 3.0 will be turned off by default in Firefox’s version 34, which is expected to be released shortly. Later versions will also support a generic TLS downgrade protection mechanism. Until then, the best preventive measure is to check the “Automatically install updates” in Firefox settings, so that you’re always on the latest version.
However, if you cannot wait for the release of Firefox 34, you can download the SSL Version Control plugin, which will automatically disable SSL 3.0, and set the more secure TLS as default.

Conclusion:
In addition to all these precautions, the concrete solution to this security vulnerability has to come from the browser vendors and site owners. Until then, you should do all you can to make sure your online browsing stays safe (till the next next severe vulnerability is find; which now seems to be happening every other day).